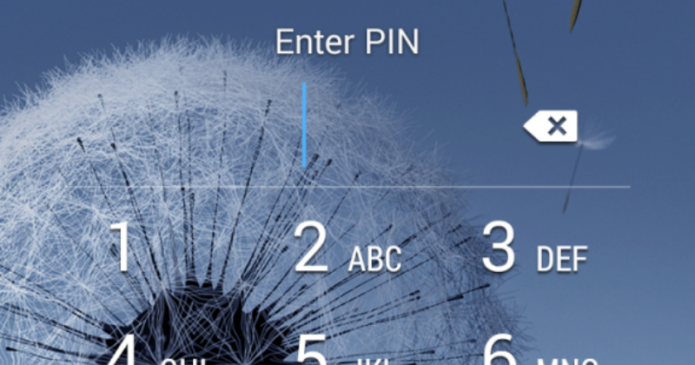
Before you get all riled up, this isn’t yet another Android vulnerability like Stagefright. This is your run of the mill malware installed through social engineering or carelessness, but one that has far graver ramifications than other ransomware. Discovered by researchers from security company ESET, the Android/Lockerpin.A ransomware goes the extra mile to actually change your device’s PIN code in such a way that trying to reset the PIN will lock the user, and ironically the attacker too, from the device completely, with no recourse other than a factory reset.
…
Read full post here:
https://www.slashgear.com/pin-changing-android-ransomware-spreading-in-the-us-11404158/